Introduction
With web security becoming a top priority for both users and search engines, Secure Sockets Layer (SSL) has become a necessity for any production application. Let’s Encrypt is a popular and free way to implement SSL encryption on your sites. When it comes to deploying applications on Kubernetes, setting up SSL might seem daunting, but automation tools like Cert-Manager simplify this process.
In this tutorial, we will go through the steps of setting up SSL with Let’s Encrypt for a web service on Kubernetes. We will use Cert-Manager, a native Kubernetes certificate management tool, to automate the issuance and renewal of SSL certificates.
Prerequisites
- An up and running Kubernetes cluster.
- kubectl command-line tool installed and configured to communicate with your cluster.
- Access to a domain name and the ability to manually edit its DNS records, or alternatively, a dynamic DNS service can be used.
Step-by-Step Instructions
Step 1: Installing Cert-Manager
kubectl create namespace cert-manager
kubectl apply -f https://github.com/jetstack/cert-manager/releases/download/v1.3.0/cert-manager.yaml
Verify the installation with:
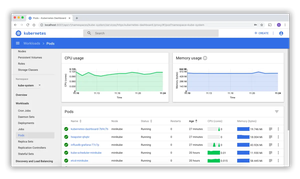
kubectl get pods --namespace cert-managerWait for the pods in the cert-manager namespace to be running before continuing to the next step.
Step 2: Setting Up Let’s Encrypt Issuer
Cert-Manager uses Issuers to manage the certificate lifecycle. Create an Issuer or a ClusterIssuer if you want to manage certificates cluster-wide.
apiVersion: cert-manager.io/v1
kind: ClusterIssuer
metadata:
name: letsencrypt-staging
spec:
acme:
server: https://acme-staging-v02.api.letsencrypt.org/directory
email: [email protected]
privateKeySecretRef:
name: letsencrypt-staging
solvers:
- http01:
ingress:
class: nginx
Modify [email protected] with your email address. The staging environment should be used first to ensure everything is set up correctly without hitting production rate limits.
Step 3: Deploying an Application
Deploy a simple web application that you want to secure with SSL using Let’s Encrypt.
apiVersion: apps/v1
kind: Deployment
metadata:
name: my-web-app
spec:
replicas: 2
selector:
matchLabels:
app: my-web-app
template:
metadata:
labels:
app: my-web-app
spec:
containers:
- name: nginx
image: nginx
ports:
- containerPort: 80
Expose the application with a service and an ingress resource that will use the Cert-Manager for SSL.
Step 4: Configuring an Ingress Resource
Create a Kubernetes Ingress resource that tells Cert-Manager to secure your application.
apiVersion: networking.k8s.io/v1
kind: Ingress
metadata:
name: my-web-app-ingress
annotations:
kubernetes.io/ingress.class: "nginx"
cert-manager.io/cluster-issuer: "letsencrypt-staging"
spec:
tls:
- hosts:
- your-domain.com
secretName: my-web-app-tls
rules:
- host: your-domain.com
http:
paths:
- path: /
pathType: Prefix
backend:
service:
name: my-web-app
port:
number: 80
Make sure to replace your-domain.com with your actual domain. The secretName will be used by Cert-Manager to store the SSL certificate for your domain.
Step 5: Testing Your Setup
Once your application is exposed and paired with an Ingress resource pointing to your domain, and after Cert-Manager has issued the certificates, you should be able to access your service over HTTPS.
Closing Thoughts
This tutorial covered the essentials of setting up SSL with Let’s Encrypt in a Kubernetes environment using Cert-Manager. Remember to switch from the staging environment to the production Let’s Encrypt server by changing letsencrypt-staging to letsencrypt-production in your Issuer resource once you’re ready to serve your application to the public.
By ensuring that your applications use SSL certificates, you not only protect your users’ data but also improve your service’s credibility and trustworthiness.