Introduction
When it comes to managing external access to the services in a Kubernetes cluster, Ingress is an API resource that controls the HTTP and HTTPS routes to services. Ingress Controllers are responsible for the implementation of the Ingress, typically a load balancer or a proxy server. In this tutorial, we will go through the steps of setting up Ingress controllers and defining Ingress rules to make your Kubernetes services accessible from outside the cluster.
Prerequisites
- A running Kubernetes cluster
- kubectl, the Kubernetes command-line tool, configured to communicate with your cluster
- Basic understanding of Kubernetes concepts like Pods, Services, and Namespaces
Step-by-Step Instructions
Step 1: Deploying an Ingress Controller
There are multiple Ingress Controllers available, but for this tutorial, we’ll focus on the popular Nginx Ingress Controller.
kubectl apply -f https://raw.githubusercontent.com/kubernetes/ingress-nginx/controller-v1.0.0/deploy/static/provider/cloud/deploy.yaml
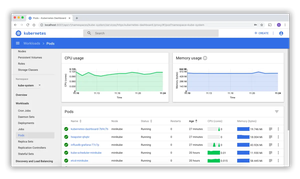
After running the command, you can check the status of the Ingress Controller pods with the following:
kubectl get pods -n ingress-nginx
Wait for the pod to be in the ‘Running’ state before moving on to the next steps.
Step 2: Defining Ingress Resources
Ingress resources define rules for routing HTTP(S) traffic to services. Let’s start with a basic Ingress resource example:
apiVersion: networking.k8s.io/v1
kind: Ingress
metadata:
name: example-ingress
namespace: default
spec:
rules:
- http:
paths:
- path: /testpath
pathType: Prefix
backend:
service:
name: test
port:
number: 80
This Ingress routes all traffic from /testpath to the ‘test’ service on port 80. Apply this Ingress resource using:
kubectl apply -f example-ingress.yaml
Confirm the Ingress was created with:
kubectl get ingress
Step 3: Securing Ingress with TLS
To secure your Ingress with TLS, you will need a TLS certificate. For this tutorial, we’ll generate a self-signed certificate (for production, you should use a certificate from a trusted CA):
openssl req -x509 -nodes -days 365 -newkey rsa:2048 -keyout tls.key -out tls.crt -subj "/CN=myapp.example.com"
Create a Secret to store the certificate and key:
kubectl create secret tls example-tls --key tls.key --cert tls.crt
Then, add the TLS configuration to your Ingress by editing example-ingress.yaml:
apiVersion: networking.k8s.io/v1
kind: Ingress
metadata:
name: example-ingress
spec:
tls:
- hosts:
- myapp.example.com
secretName: example-tls
rules:
- host: myapp.example.com
http:
paths:
- path: /secure
pathType: Prefix
backend:
service:
name: secure-service
port:
number: 443
Apply the changes to the Ingress:
kubectl apply -f example-ingress.yaml
You can now access your service over HTTPS using your browser or curl, verifying that the TLS termination is happening correctly.
Advanced Ingress Features
As you get more familiar with Kubernetes and Ingress, you might want to use some of the more advanced features, such as setting up a default backend for handling 404 errors, rewriting the request path before it reaches the backend service, or using annotations to modify Ingress behavior.
Default Backend
apiVersion: networking.k8s.io/v1
kind: Ingress
metadata:
name: example-ingress
spec:
defaultBackend:
service:
name: default-service
port:
number: 80
Path Rewriting
In the Nginx Ingress Controller, you can use annotations to rewrite paths. Edit example-ingress.yaml:
apiVersion: networking.k8s.io/v1
kind: Ingress
metadata:
name: example-ingress
annotations:
nginx.ingress.kubernetes.io/rewrite-target: /$1
spec:
rules:
- http:
paths:
- path: /rewrite/(.*)
pathType: Prefix
backend:
service:
name: rewritten-service
port:
number: 80
Conclusion
Setting up Ingress Controllers and defining Ingress rules are essential for routing external traffic into the services within your Kubernetes cluster. Once properly configured, your Ingress resources can offer advanced traffic management features, better performance, and improved security through TLS termination and other mechanisms.